🛠 SBOM: lightweight cdxgen generation
Earlier, we looked here at what the Software Bill of Materials SBOM is. We looked at what it looks like, why it is used, and why it is used. Let's now look at the tool itself and how to use it, but it has some special features.
Tool:
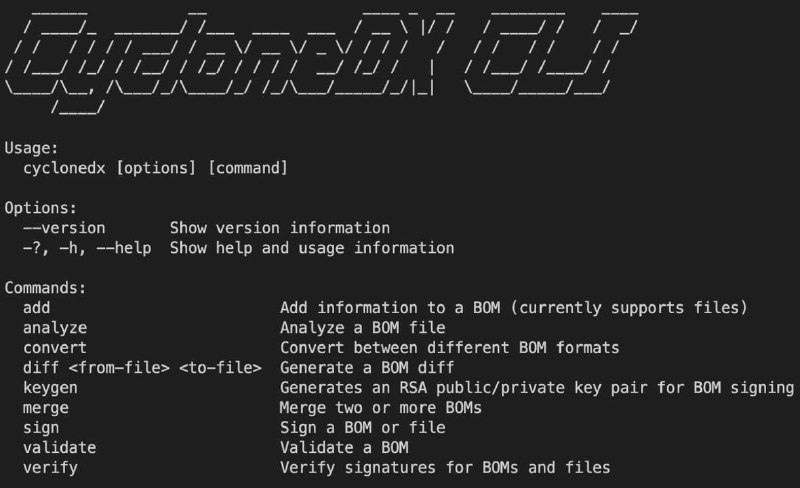
cdxgen - CLI tool for SBOM automation in CycloneDX format. Basic functions such as analyzing metadata and licenses, reading manifest files. The only important thing it has is the generation of one format. License type: Apache License 2.0.
Converting SBOM to a format other than CycloneDX will require a converter. Dependencies collected manually or repackaged may not be determined or partially determined. Compatible with Dependency-Track for SBOM management, including Trivy, Grype.
Supports the following languages and package formats. Official documentation and repository. Can sign them.
Application:
sudo npm install -g @cyclonedx/cdxgen
cd <Path to source code>
docker run --rm -e CDXGEN_DEBUG_MODE=debug -v /tmp:/tmp -v $(pwd):/app:rw -t ghcr.io/cyclonedx/cdxgen:master -r /app -o /app/bom.json # or -p for console/terminal output
cdxgen -t java -o bom.json --server-url https://deptrack.server.com --api-key "token" --project-group ... # example of sending to Dependency-Track
Flags:
cdxgen [-t], [-o], [-p], [-r], [-h], [-v]
-t, --type # if you do not specify this parameter, it will collect all the dependencies that it can
--exclude-type # remove from processing
-o, --output # saving in format - XML, JSON
-p, --print # output the "SBOM tree" as a table
-r, --recurse // recursive scanning of directories
--no-recursive # based on files in the root directory
--deep
--fail-on-error # if collection of one of the types fails, the component displays earning
--technique # The default is auto mode, but you can set "source-code-analysis", "binary-analysis", "manifest-analysis", "hash-comparison", "instrumentation", "filename"
--required-only # for exceptions/limitations
Supported BOMs:
• Cryptography CBOM - Java, Python
• Operations OBOM - Linux container images
• Software-as-a-Service SASBOM - Java, Python, JavaScript, TypeScript, PHP
• Attestations (CDXA)
• Vulnerability Disclosure Report (VDR) - OWASP depscan VDR
Pipeline:
sbom:
image: node:20-alpine
stage: test
script:
- npm i -g @cyclonedx/cdxgen
- cdxgen -r . -o sbom.json
artifacts:
paths: [sbom.json]
Overall: the tool is quite simple, it will help collect dependencies and control them, for example, it is useful for checking the components used in the project and when merging/pull requesting from a contributor. And yes, of course, the favorite story is setting the path for the registry and using only safe dependencies.
#toolchain #sbom