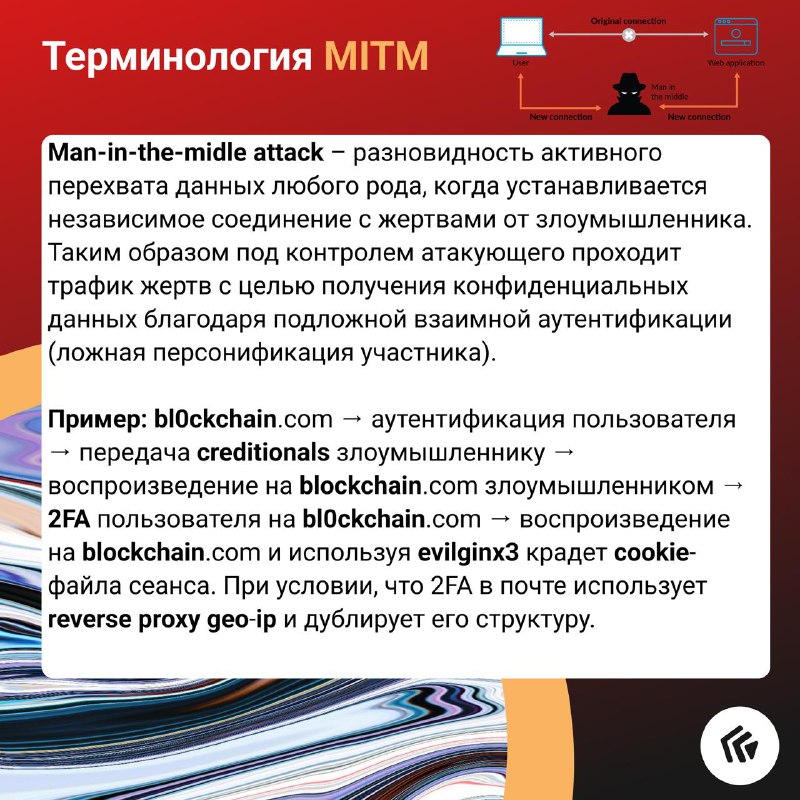
🤔 MITM Terminology
Salute,
I thought it would be cool to see posts with terminology that will allow you to broaden your horizons and be more conscious about your wording.
We will take an atypical base, as usual, but we will still touch on something classic. Next we will consider some of them in more detail.
Let's start with the "man in the middle" attack and note that there are such types as:
- WiFi eavesdropping
- "Evil Twin"
- Rogue access point
- "Man-in-the-browser"
- Session interception (discussed in the example)
- Packet sniffing
- and so on
#term #pmcases